
Your 2022 security protocols are the biggest threat to your 2026 balance sheet. While bespoke software provides the scalability your business demands, legacy code often hides vulnerabilities that modern regulators no longer overlook. You likely recognize that staying ahead of gdpr compliance is a moving target, yet the friction between legal theory and actual technical implementation remains a significant hurdle for most development teams.
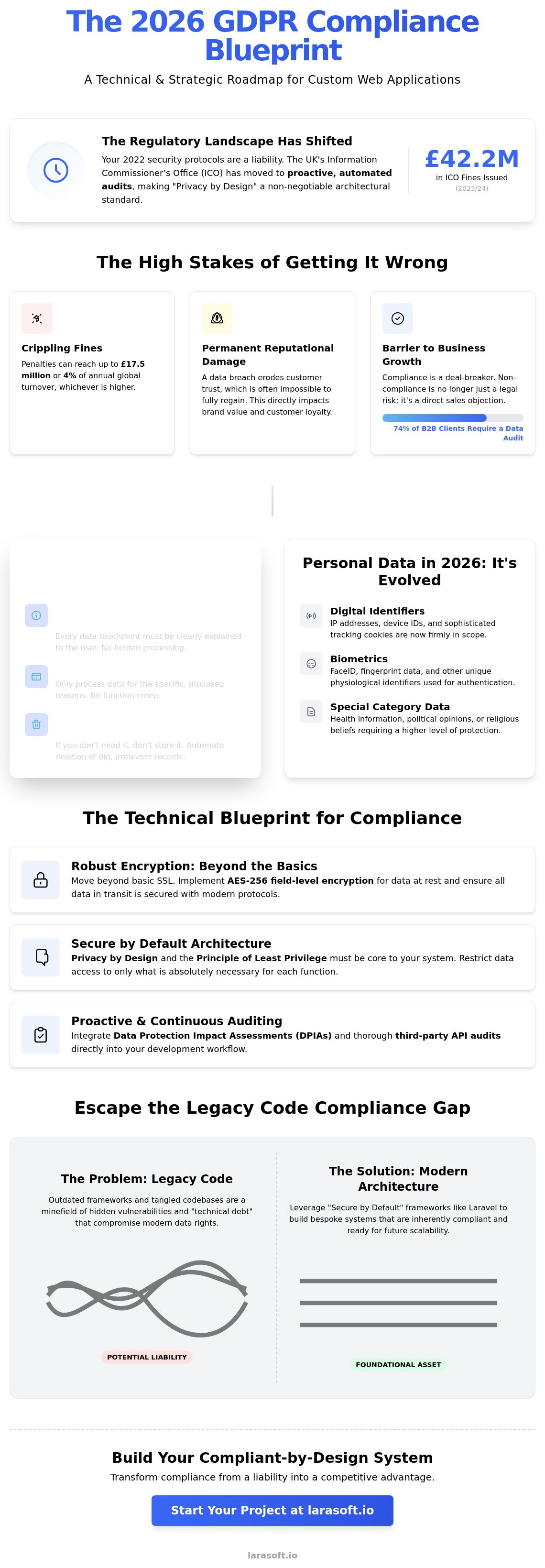
We've engineered this guide to remove that uncertainty. You'll find a comprehensive technical and strategic checklist designed to align your data architecture with current UK GDPR standards. By following this roadmap, you can secure your application against the types of breaches that led the ICO to issue £42.2 million in fines during the 2023/24 financial year. We will examine the specific code level adjustments and architectural shifts necessary to transform your software from a potential liability into a verified foundational asset for your future growth. This overview covers everything from database encryption protocols to automated data retention scripts.
The regulatory environment for custom web applications has matured significantly since the initial rollout of data protection laws. In 2026, gdpr compliance is no longer a checkbox exercise completed at the end of a project; it's a fundamental architectural requirement. For UK-based software, the complexity lies in the dual-layered approach of the UK GDPR and the EU GDPR. While they share a common lineage, the General Data Protection Regulation (GDPR) remains the definitive standard that governs how bespoke platforms handle cross-border data flows. Aligning with both ensures your application can scale internationally without hitting legal roadblocks.
The Information Commissioner’s Office (ICO) has shifted its 2026 enforcement strategy toward proactive, automated audits of high-growth digital platforms. They no longer wait for a breach to occur before investigating. They focus on how data is structured within your application's database. This makes "Privacy by Design" the mandatory standard for any custom build. You can't bolt privacy onto a finished product. It must exist within the API integrations, the database schema, and the user authentication flows from day one.
Ignoring these standards carries heavy penalties. Beyond the statutory fines of up to £17.5 million or 4% of annual global turnover, the reputational damage is often permanent. A 2025 industry report indicated that 74% of B2B clients now require a comprehensive data protection audit before signing contracts for custom software services. Non-compliance isn't just a legal risk; it's a barrier to business growth.
Successful gdpr compliance relies on three core pillars in your software's logic. First, lawfulness, fairness, and transparency require that every data touchpoint is clearly explained to the user. Second, purpose limitation ensures your application only processes data for the specific reasons you've disclosed. Finally, data minimisation and storage limitation force developers to prune old records. If your Laravel application doesn't need a user’s phone number to function, don't store it. If a record is three years old and serves no purpose, your system should automatically archive or delete it.
The scope of personal data has expanded. In 2026, it includes much more than names and email addresses. Your application's architecture must account for:
Modern software architecture differentiates between pseudo-anonymous data (which can be re-linked to a person) and truly anonymous data. For 2026 compliance, your developers must ensure that any analytics or reporting tools utilize true anonymization to remove the application from the strictest regulatory burdens where possible.
Building a secure application in 2026 requires a shift from reactive patches to privacy by design. While basic SSL certificates were the standard a decade ago, modern gdpr compliance mandates a deeper architectural commitment to data integrity. This involves layering security protocols directly into the application's source code rather than relying solely on server-side configurations. According to the official guide on the technical pillars of a compliant application, developers must ensure that security is a core component of the entire development lifecycle.
We focus on a "Least Privilege" architecture. This means every module, service, and user account has access only to the specific data it needs to function. By restricting these permissions, we limit the potential blast radius of a security incident. When we build custom systems, we replace broad administrative access with granular controls that log every interaction, providing an immutable audit trail that's essential for regulatory reporting.
Standardizing on AES-256 for database encryption is the baseline for protecting sensitive information at rest. We implement this at the field level to ensure that even if a database breach occurs, the raw data remains unreadable without the specific decryption keys. Secure API integration is equally vital; we use OAuth 2.0 and scoped tokens to protect data as it moves between internal microservices or third-party platforms. End-to-end encryption for web apps ensures that sensitive information is encrypted on the client side and only decrypted by the authorized recipient, keeping it invisible to server administrators. This level of technical precision is why many growing businesses partner with Laravel specialists who prioritize clean, secure code architecture.
Automation is the only way to handle the 30-day window for Subject Access Requests (SAR) efficiently as your user base scales. We build dedicated SAR tools into the admin panel, allowing your team to generate a full report of a user's data with a single click. For data portability, users should have self-service access to export their info in machine-readable JSON or CSV formats. This reduces the manual burden on your support staff while empowering the end user.
Consent management has also evolved significantly. The 2026 standard moves away from "Accept All" banners toward granular opt-ins. You must allow users to toggle specific categories of data processing, such as marketing or analytics, without losing access to the core application. To meet "Right to Erasure" requests, we implement automated data deletion workflows. These scripts identify and purge user records across all linked tables, including backups and third-party logs, within the 72-hour window often expected for high-priority cases. This prevents "ghost data" from lingering in legacy reporting modules and ensures your gdpr compliance remains absolute.
Building a custom application in 2026 requires more than basic encryption; it demands a structural commitment to gdpr compliance. As regulatory scrutiny intensifies, bespoke software must be engineered with privacy as a foundational layer rather than an afterthought. This checklist focuses on the technical and operational benchmarks required to maintain a secure, compliant ecosystem.
Success depends on human protocol as much as clean code. Assign a Data Protection Officer (DPO) or a dedicated lead contact to oversee data governance. Your team needs a 72-hour data breach notification protocol that's been stress-tested through simulated drills. Regular staff training on secure data handling within your specific software environment prevents the human errors that cause 82% of modern data leaks.
Maintain an up-to-date Record of Processing Activities (ROPA) to track how data moves through your system. We recommend mapping data flows across the frontend, Laravel backend, and all external APIs to identify potential bottlenecks or exposure points. Documenting every security patch and software maintenance schedule creates a paper trail of "state of the art" protection, which is a primary defense in gdpr compliance audits.
Legacy code is the silent killer of gdpr compliance. Outdated frameworks account for 76% of vulnerabilities in modern web applications according to 2024 security research. These systems were often built before "Privacy by Design" became a legal standard, leaving them ill-equipped for 2026 requirements. When your core architecture is brittle, implementing modern data rights feels like performing surgery with a sledgehammer.
Old code creates a technical debt trap. If your system can't isolate and delete a single user's data within the 30-day GDPR window without breaking dependencies, you've inherited a massive liability. This rigidity prevents the automation of data portability and erasure requests. It forces your team into manual work that is prone to human error and missed deadlines.
Unmaintained databases often harbor "shadow data." These are forgotten tables, temporary logs, or abandoned columns containing PII that your current team might not even know exists. A 2023 Veritas report found that 33% of corporate data is redundant, obsolete, or trivial. In a legacy environment, this hidden data is a ticking time bomb for regulators. Choosing "patch-and-pray" tactics over strategic modernization is no longer viable. Clean, refactored code isn't just a technical preference; it's a legal necessity.
Refactoring legacy authentication is the first priority. We replace hard-coded login logic with modern standards like OpenID Connect or OAuth2. Migrating data to encrypted environments using AES-256 ensures that even if a breach occurs, the data remains unreadable. An API-first architecture simplifies gdpr compliance by centralizing data access. This allows you to control exactly what data is exposed and to whom, creating a transparent audit trail that legacy monoliths can't match.
Software maintenance is directly linked to legal liability under GDPR Article 32. Running "End of Life" (EOL) frameworks, such as PHP 7.4 or early 8.x versions, signals a failure of technical due diligence. If a breach occurs on an unsupported platform, regulators view it as negligence. The 2023 IBM Cost of a Data Breach Report noted the average breach cost hit $4.45 million. Investing in a modern Laravel-based refactor typically costs less than 5% of that potential fine, making modernization the most logical business decision you can make this year.
Achieving gdpr compliance in 2026 demands a technical foundation that treats data privacy as a core architectural requirement rather than a final layer of polish. Larasoft utilizes the Laravel framework to provide a "Secure by Default" environment for UK businesses. This choice isn't accidental. Laravel’s built-in protection against SQL injection, cross-site request forgery, and cross-site scripting provides a robust shield from day one. We don't just build features; we construct resilient digital ecosystems that protect your reputation.
Our development process begins with a rigorous discovery and architecture phase. We map every data touchpoint to ensure the principle of data minimization is upheld. By defining clear data retention policies and encryption standards at the blueprint stage, we prevent the structural vulnerabilities that lead to breaches. It's about technical precision. We ensure your application architecture supports the right to be forgotten and data portability requests without requiring manual, error-prone intervention from your team.
We leverage Laravel's native encryption and hashing features to secure your most sensitive information. Using OpenSSL and AES-256 or AES-128 encryption, we ensure data remains unreadable even if the physical storage is compromised. Our team specializes in bespoke API development, where security is the primary driver. We implement Laravel Sanctum or Passport to provide hardened, token-based authentication for every integration. To stop security regressions before they start, we provide proactive software maintenance that includes:
Moving away from legacy systems is a critical step for modern compliance. We transform outdated platforms into future-proof Laravel applications that grow with your business. We don't just act as a service provider; we're a technical ally invested in your stability. Your vision, our code. This partnership ensures that as gdpr compliance standards evolve, your software adapts alongside them. We treat your code as a foundational asset, ensuring it remains scalable and secure for years to come. Contact Larasoft today for a GDPR-focused technical audit and ensure your web application is ready for the challenges of 2026.
Maintaining gdpr compliance in the 2026 digital landscape requires more than a simple privacy policy update. It demands a rigorous shift toward bespoke "Privacy by Design" architecture that handles data at the schema level. As regulatory bodies increase scrutiny on automated processing, your custom application's technical foundation becomes its strongest defense. Addressing the legacy code gap isn't just a security measure; it's a strategic necessity for long-term business continuity.
LaraSoft operates as your dedicated technical ally. We're UK-based Laravel specialists with deep expertise in high-security legacy code modernisation. We don't just patch systems; we engineer scalable solutions built on clean, efficient code that protects your users and your reputation. Our team transforms complex technical requirements into a structured journey toward growth. We take pride in building systems that work perfectly under pressure while adhering to the highest standards of craftsmanship.
Don't leave your application's security to chance. Request a GDPR Technical Audit for Your Application today. We'll help you build a resilient system that's ready for the future. Your vision deserves the protection of our code.
The maximum fine for a 2026 GDPR breach remains €20 million or 4% of your total global annual turnover from the preceding financial year, whichever is higher. These penalties apply to Tier 2 infringements under Article 83(5) of the regulation. Regulators prioritize the severity and duration of the breach when calculating the final amount. Maintaining strict gdpr compliance within your application architecture is the only way to mitigate these catastrophic financial risks.
Yes, every UK business that processes personal data must comply with the UK GDPR and the Data Protection Act 2018. Size doesn't grant an exemption from these legal requirements. If your custom application handles names, emails, or IP addresses of UK or EU residents, you're legally bound to protect that information. Failure to comply can lead to investigations by the Information Commissioner’s Office (ICO), regardless of your company's headcount.
A Data Controller determines the purposes and means of processing personal data, while a Data Processor handles data only on the Controller's behalf. If you're building a bespoke application to manage your customers, you're the Controller. The cloud hosting provider you select acts as the Processor. It's vital to have a clear Data Processing Agreement (DPA) between both parties to define these legal boundaries and ensure accountability for every data touchpoint.
You can only store user data for as long as it's necessary for the specific purpose you originally identified during collection. Article 5(1)(e) doesn't set a universal expiration date, so you must define your own retention periods. For example, financial records are typically kept for 6 years to meet UK tax laws. We build automated data pruning scripts into our software to delete expired records systematically and reduce your liability.
You're required to appoint a DPO if your core activities involve large-scale systematic monitoring or processing of sensitive special category data. While most small software projects don't meet this threshold, Article 37 mandates a DPO for all public authorities. If your application processes health data for thousands of users, you'll need this specialized role to oversee your data protection strategy and ensure ongoing regulatory alignment with evolving standards.
Laravel is not inherently compliant, but it provides a robust toolkit to build a secure, compliant application. Our specialists leverage Laravel's native features like Bcrypt password hashing, AES-256 encryption, and automated CSRF protection to secure your data. While the framework handles the technical foundation, your specific business logic and data handling workflows must be audited to ensure full gdpr compliance across the entire user journey.
You're legally responsible for the data you collect, even if the breach occurs within a third-party API. Under Article 33, you must notify the relevant supervisory authority within 72 hours of becoming aware of the incident. We mitigate this risk by conducting rigorous due diligence on all API integrations and implementing robust logging to detect external failures before they compromise your system or result in regulatory scrutiny.
You must respond to a Subject Access Request within 30 days by providing a copy of the individual's data in a machine-readable format. For complex custom applications, this requires exporting data from multiple database tables and linked services. We design bespoke export tools that aggregate this information into a single JSON or CSV file, ensuring you meet the legal deadline without performing manual, error-prone data mining tasks.
Here’s what we've been up to recently.
Certified Quality. Great Prices